others-How to solve 'no matching key exchange method found' issue when using git commands ?
1. Purpose
In this post, I would demo how to solve the below issue when using git pull command :
Unable to negotiate with 10.1.1.2: no matching key exchange method found.
Their offer: diffie-hellman-group1-sha1
fatal: Could not read from remote repository.
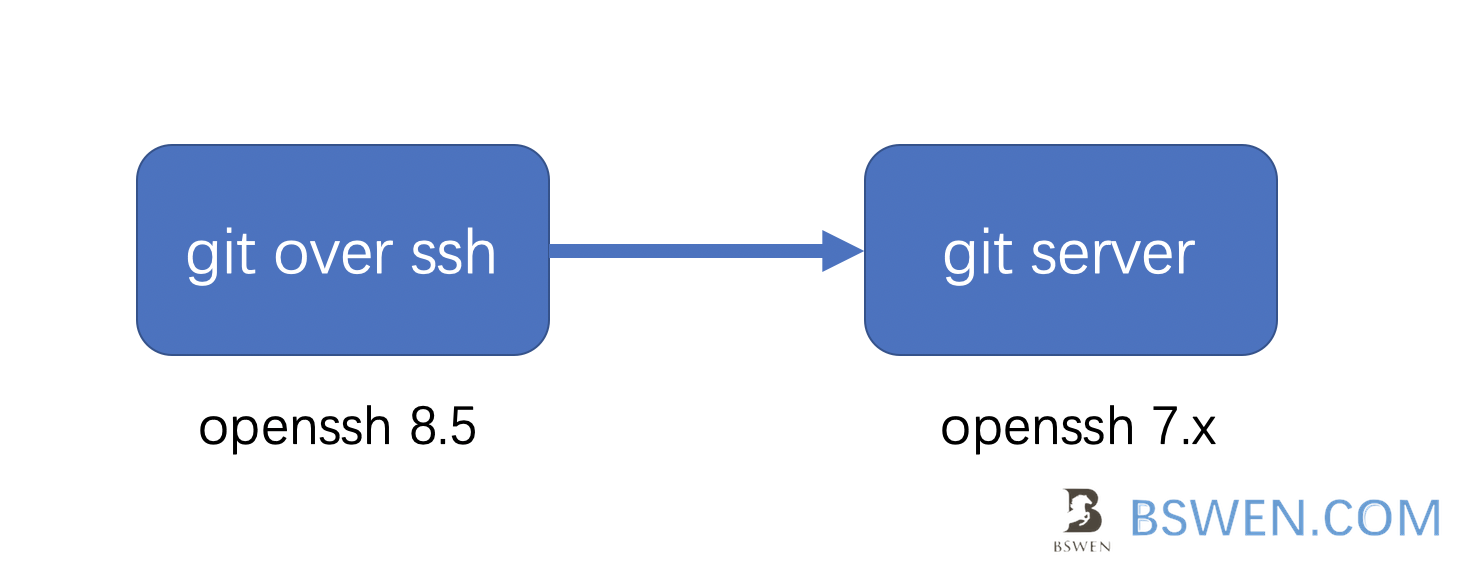
2. Environment
- client openssh version: OpenSSH_8.5
- server openssh version: OpenSSH_7
3. The problem and solution
3.1 The problem
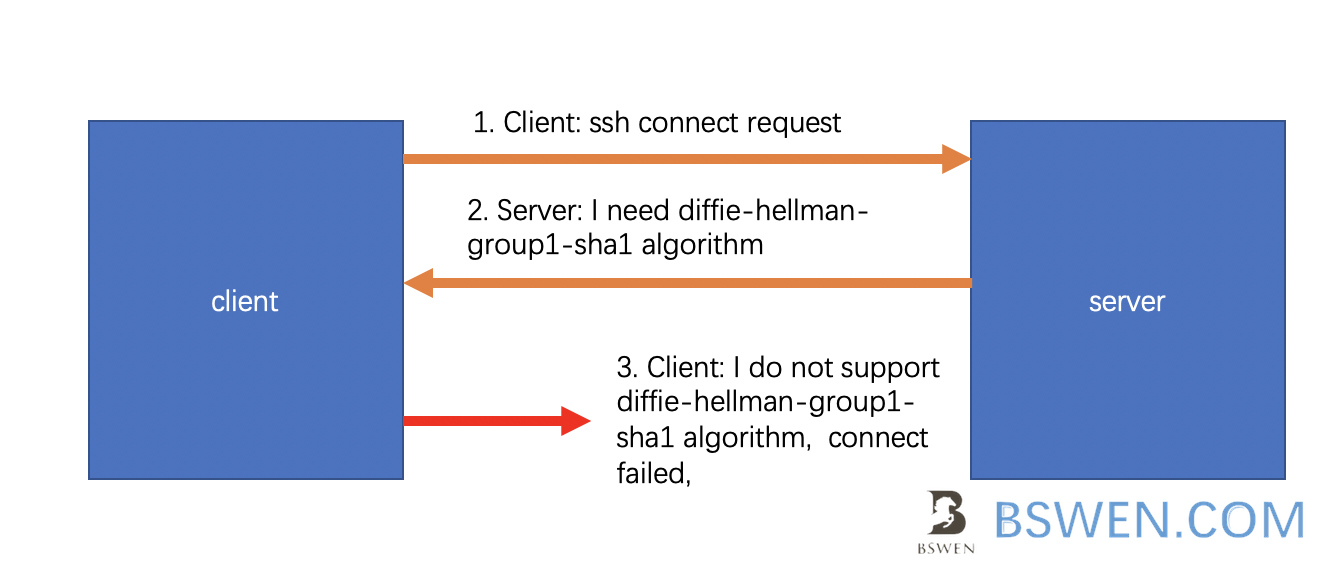
When we want to execute git pull or git clone command over SSH to git server, if the versions of openSSH do not match, the problem would occur.
Just as the above picture shows, if we connect the server with a higher version of openssh, the following error would occur:
Unable to negotiate with 10.1.1.2: no matching key exchange method found.
Their offer: diffie-hellman-group1-sha1
fatal: Could not read from remote repository.
3.2 Debug
We can debug the issue with following commands:
$ GIT_SSH_COMMAND="ssh -vvv" git pull
OpenSSH_8.5, OpenSSL 1.1.1k 12 Mar 2021
debug1: Reading configuration data ...
3.3 The solution
The problem is caused by the mismatched key exchange algorithm of openssh, the error message indicates that the algorithm diffie-hellman-group1-sha1 is required by server, but it is not supported locally, we can just configure the local openssh to support this algorithm.
Open your ~/.ssh/config file,and configure like this: (Suppose your server’s ip address is 10.1.1.2)
Host 10.1.1.2
KexAlgorithms +diffie-hellman-group1-sha1
Execute the git command again:
➜ bswen git:(master) ✗ git pull
Already up to date.
➜ bswen git:(master) ✗
Now it works!
3.4 Why did this happen?
When git client tries to connect to git server, it actually uses the ssh protocol, the problem is caused by the algorithm mismatch of both sides.
When an SSH client connects to a server, each side offers lists of connection parameters to the other. These are, with the corresponding ssh_config keyword:
KexAlgorithms: the key exchange methods that are used to generate per-connection keysHostkeyAlgorithms: the public key algorithms accepted for an SSH server to authenticate itself to an SSH clientCiphers: the ciphers to encrypt the connectionMACs: the message authentication codes used to detect traffic modification
For a successful connection, there must be at least one mutually-supported choice for each parameter.
If the client and server are unable to agree on a mutual set of parameters then the connection will fail. OpenSSH (7.0 and greater) will produce an error message like this:
Unable to negotiate with legacyhost: no matching key exchange method found.
Their offer: diffie-hellman-group1-sha1
In this case, the client and server were unable to agree on the key exchange algorithm. The server offered only a single method diffie-hellman-group1-sha1. OpenSSH supports this method, but does not enable it by default because it is weak and within theoretical range of the so-called Logjam attack.
Why diffie-hellman-group1-sha1 is not supported in newer openssh versions? This algorithm is considered not secure so it’s removed from newer versions of openssh.
You can get more information about this change on this website.
4. Summary
In this post, I tried to demo how to solve the no matching key exchange method found error when trying to use SSH protocol to connect to an SSH server, the key point is that both sides of the communication must have at least one common algorithm to connect successfully.